Motivation
Policy Reporter was created to make the results of your Kyverno validation policies more visible and observable. By default, Kyverno provides the option to create your validation policies in audit or enforce mode. While enforce blocks to applying a manifests that violate the given policy, audit creates PolicyReports that provide information about all resources that pass or fail your policies. Because Policy Reports are simple Custom Resource Definitions you can access them with kubectl get/describe.
The disadvantages of these PolicyReports are that the results of a policy can be spread across multiple namespaces and both, the passed and failed results of multiple policies, are combined into one PolicyReport. This makes it difficult to find all failed results of a single ClusterPolicy. Since a PolicyReport contains all the results of a namespace, it is also difficult to check for new violations by new policies or resources.
Policy Reporter helps with this problems by providing different features based on PolicyReports:
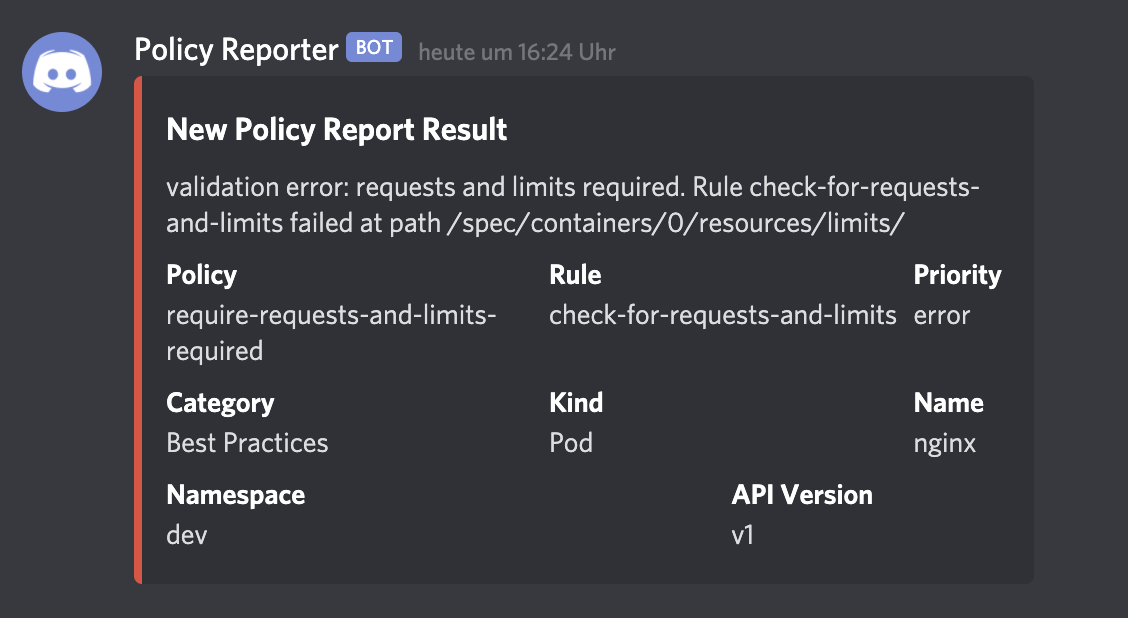
- New violations can be send to different clients like Grafana Loki, Elasticsearch, Slack, Discord or MS Teams
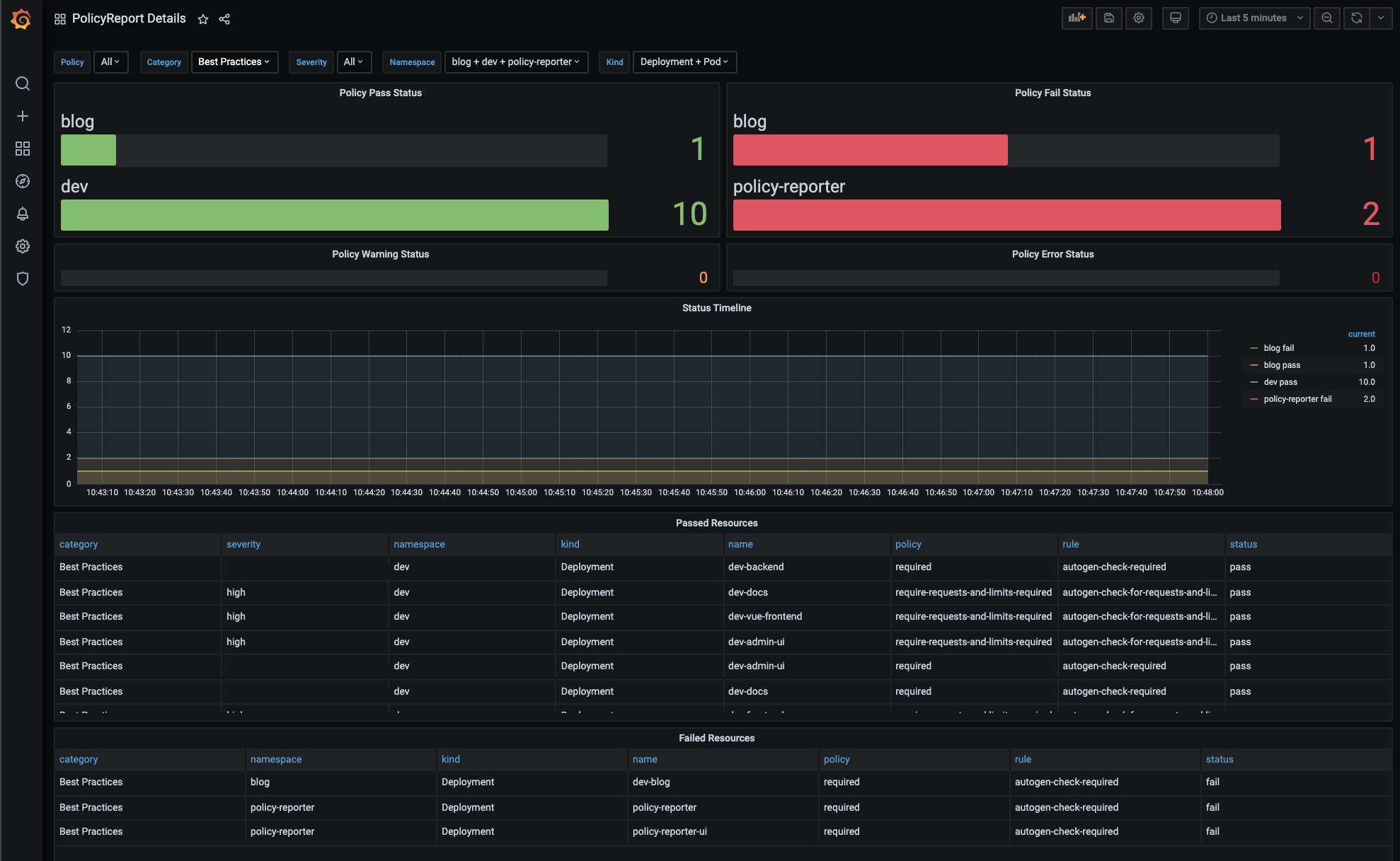
- The optional metrics endpoint can be used to observe violations in monitoring tools like Grafana
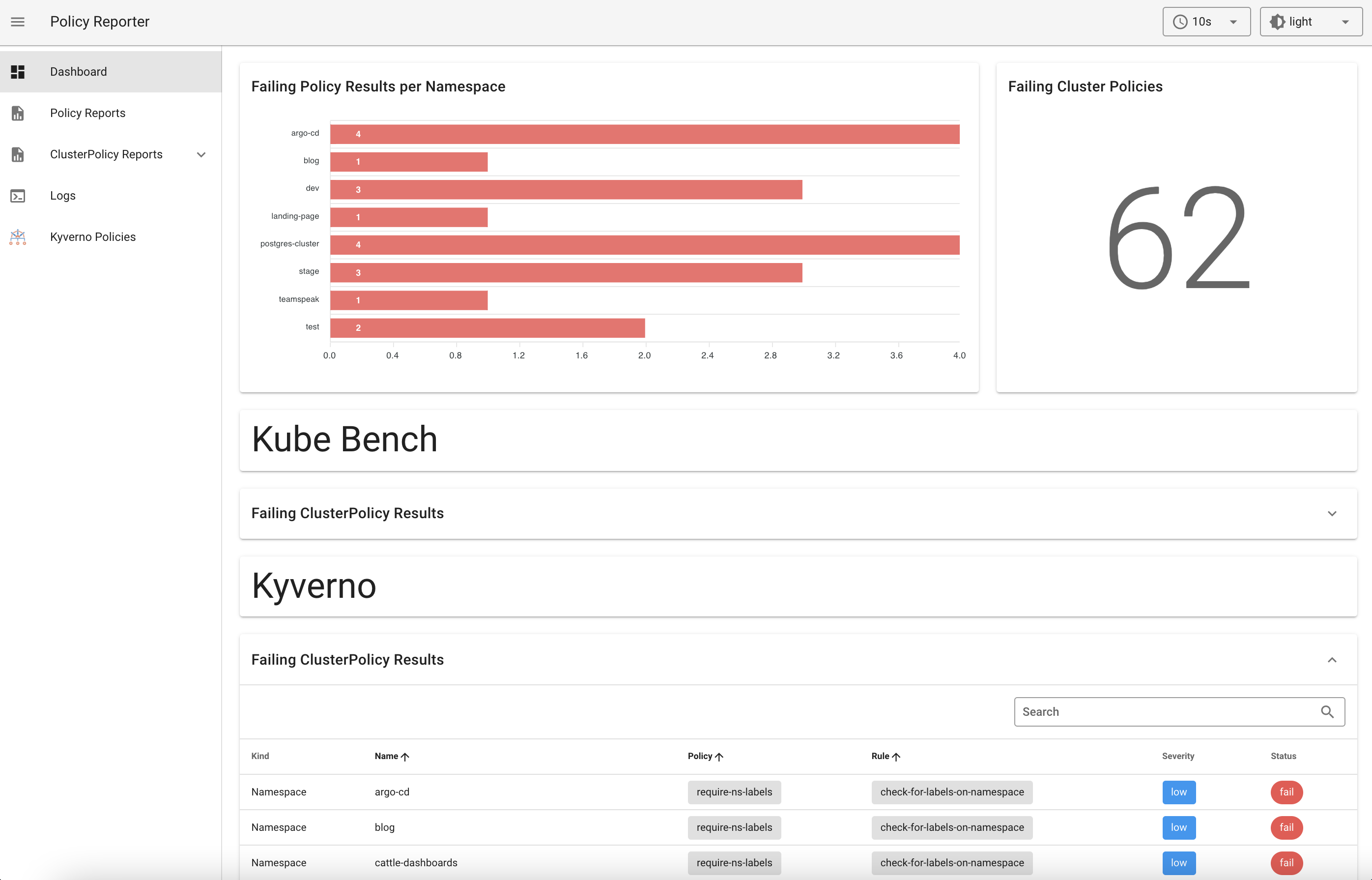
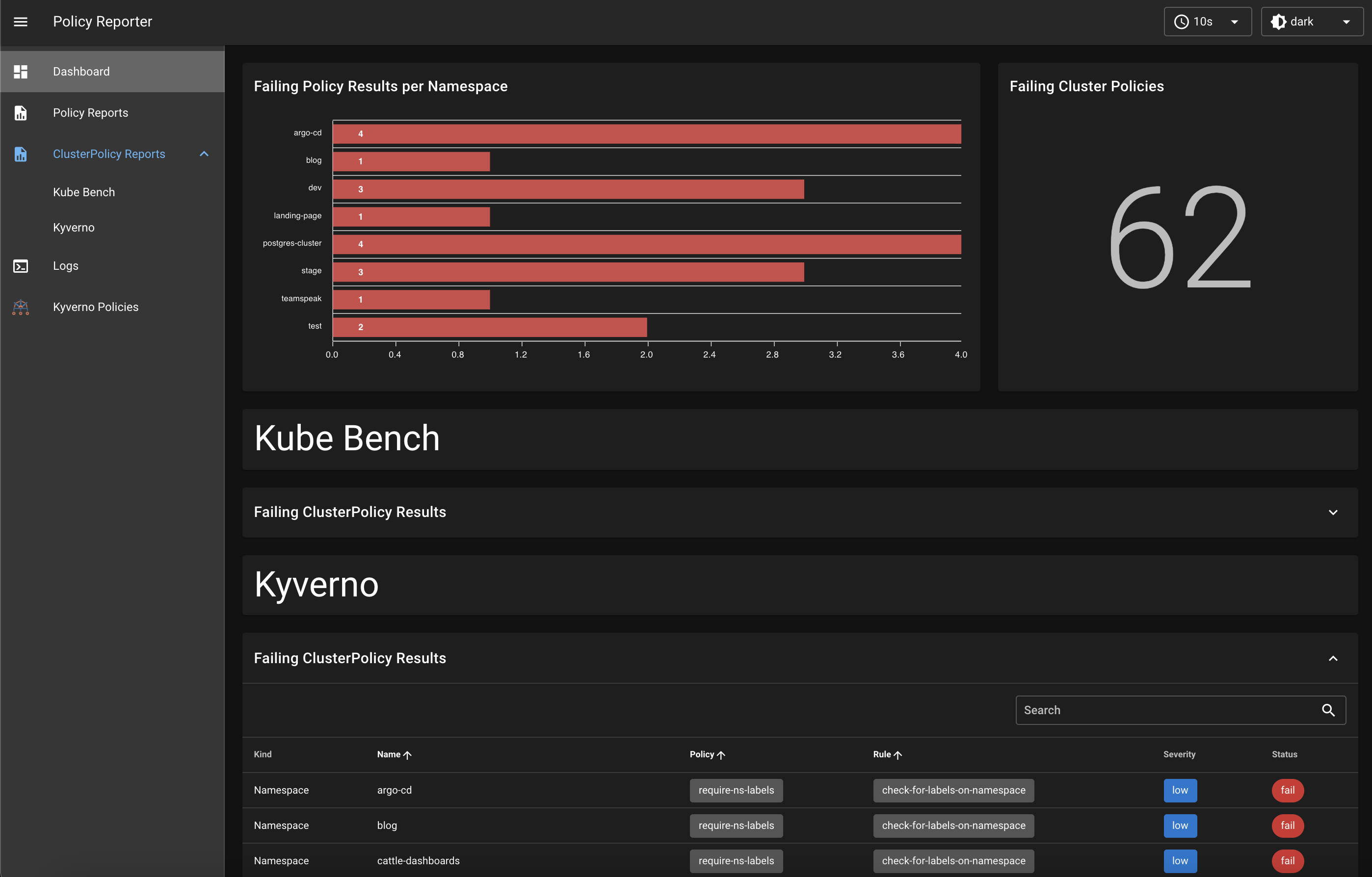
- Policy Reporter provides also a standalone Dashboard to get a graphical overview of all results with filter and an optional Kyverno Plugin to get also information about your Kyverno policies.
Use cases
Due to the work of the Kubernetes Policy Working Group and Community, the adoption of the PolicyReport and ClusterPolicyReport CRDs for different apps is increasing. This enables Policy Reporter to be used with other tools such as Kube Bench, Trivy, jsPolicy or Falco.
Screenshots
Policy Reporter UI
Grafana
Discord
Resources
Videos
Blogs
- [07.04.2021] Monitor Security and Best Practices with Kyverno and Policy Reporter
- [28.02.2022] Kubernetes Security — Use Kyverno Policy Reporter to fix Kyverno deployment by Charles-Edouard Brétéché
- [02.10.2022] Whats new in Policy Reporter
- [07.12.2022] PoC! — Kyverno & Policy Reporter UI on Openshift 4.x by Tommer Amber

